The world of cryptocurrency is vast, with numerous algorithms and coins vying for attention. Among these, the X11 algorithm stands out, not just for its technical prowess but also for its unique approach to decentralization and security. In this section, we’ll delve deep into the origins, significance, and the unique features of X11 coins.
What is the X11 Algorithm?
The X11 algorithm is a unique hash function that was designed for the Dash cryptocurrency. Named for its use of 11 different cryptographic functions, X11 is a chained hashing approach, which means it applies not one, but 11 sequential rounds of hashes (hence the name X11). The 11 individual algorithms that make up X11 are:
| Algorithm | Purpose |
|---|---|
| BLAKE | High-speed cryptographic hashing |
| BLUE MIDNIGHT WISH | Optimized for 64-bit platforms |
| Grøstl | Provides security against all known attack methods |
| JH | Designed to provide a high level of security |
| Keccak | Known for its sponge construction |
| Skein | Uses a unique Threefish tweakable block cipher |
| Luffa | A wide-pipe hash function |
| CubeHash | A cryptographic hash function |
| SHAvite-3 | A fast, efficient algorithm |
| SIMD | Optimized for parallel processing |
| ECHO | Designed for efficient memory usage |
Why X11 Coins Matter?
The inception of X11 was not just a technical endeavor but also a strategic one. Evan Duffield, the core developer of Dash (previously known as Darkcoin), introduced X11 as a response to concerns about the centralization of mining. With the rise of ASIC (Application Specific Integrated Circuit) miners, which are powerful machines designed specifically for mining, there was a growing fear that mining power would become concentrated in the hands of a few, undermining the decentralized ethos of cryptocurrencies.
X11 was designed to be ASIC-resistant, at least initially. This means it was intended to level the playing field, allowing individual miners using regular CPUs and GPUs to participate in the mining process without being overshadowed by powerful ASICs.
However, as with many things in the fast-evolving world of cryptocurrencies, the landscape changed. But that initial intent, combined with the robustness of the X11 algorithm, has left an indelible mark on the crypto community.
Brief history of X11 algorithm
The X11 algorithm didn’t just appear out of thin air. Its creation was a calculated move, a response to the evolving landscape of cryptocurrency mining. Let’s journey back to its roots and understand the motivations behind its inception.
A Response to ASIC Dominance
By the time X11 was introduced, the cryptocurrency world was already familiar with the power and dominance of ASIC miners. Bitcoin, the pioneer of cryptocurrencies, utilized the SHA-256 algorithm, and Litecoin, another popular coin of the time, was based on the Scrypt algorithm. Both these algorithms eventually fell prey to ASIC miners, leading to concerns about centralization.
ASIC miners, with their superior hashing power, began to dominate the mining scene. This posed a significant threat to the decentralized nature of cryptocurrencies. With ASICs in play, individual miners using traditional CPUs and GPUs found it increasingly challenging to compete. The dream of a decentralized network, where every participant had an equal opportunity, seemed to be fading.
Evan Duffield’s Vision
Enter Evan Duffield and his vision for Dash. Duffield wasn’t just looking to create another cryptocurrency; he aimed to address the growing concerns about ASIC dominance. His solution? The X11 algorithm.
Designed by Duffield, X11 was a departure from the traditional single-hash approach. By chaining together 11 different cryptographic functions, Duffield hoped to create an algorithm that was not only secure but also resistant to the looming threat of ASICs. The multi-hash approach was intended to add complexity, making it difficult for ASIC developers to create hardware specifically for X11 mining.
The Birth of Dash and Beyond
With the X11 algorithm as its backbone, Dash (initially known as Darkcoin) was launched. The coin quickly gained traction, not just for its privacy features but also for its promise of a more egalitarian mining process. For a while, X11 lived up to its promise, providing a haven for GPU and CPU miners.
However, the world of technology is one of constant evolution. Despite its initial ASIC-resistant design, X11 eventually saw the introduction of ASIC miners tailored for its complex structure. But that’s a story for another section.
Why ASIC Resistance Matters
To truly appreciate the significance of X11’s initial ASIC-resistant design, it’s essential to understand the broader context of ASICs and their impact on the cryptocurrency ecosystem. This section will shed light on the importance of ASIC resistance and why it has been a focal point for many within the crypto community.
The Rise of ASICs
ASIC, which stands for Application Specific Integrated Circuit, is a type of hardware designed for a specific task. In the world of cryptocurrencies, ASICs are tailored to mine specific algorithms at lightning speeds. Their introduction marked a significant shift in the mining landscape.
Initially, cryptocurrencies like Bitcoin could be mined using regular personal computers. As the rewards for mining were lucrative, there was a surge in participants. However, as more miners joined the network and the mathematical problems to validate transactions became more complex, the need for more computational power grew.
Enter ASICs, with their unparalleled hashing capabilities. These machines could solve cryptographic puzzles at a much faster rate than traditional CPUs and GPUs. While this might sound like a technological advancement, and in many ways it was, it also brought with it a set of challenges.
Centralization vs. Decentralization
The core ethos of cryptocurrencies is decentralization, a system where no single entity has overwhelming control. However, ASICs, due to their cost and efficiency, started to tilt the balance. Those who could afford these powerful machines had a distinct advantage, leading to a concentration of mining power in the hands of a few. This centralization of hashing power raised alarms, as it went against the very principles on which cryptocurrencies were built.
A more centralized system is not only contrary to the democratic spirit of cryptocurrencies but also poses security risks. With more power in fewer hands, the network becomes vulnerable to ‘51% attacks’, where a single entity with the majority of the network’s hashing power can double-spend coins and carry out fraudulent activities.
The X11 Promise
In this backdrop, the X11 algorithm emerged as a beacon of hope. Its multi-hash design was seen as a countermeasure to ASIC dominance. By making the mining process more complex and layered, the idea was to deter the development of ASICs tailored for X11, at least for a while.
Evolution of X11: From ASIC Resistance to ASIC Dominance
The tale of X11 is one of innovation, ambition, and the inexorable march of technology. While its inception was rooted in a vision of decentralization and egalitarianism, the realities of technological advancement presented challenges that reshaped the X11 landscape.
The Inevitability of Progress
Despite the intricate design of the X11 algorithm, the allure of its potential rewards made it a prime target for hardware developers. The promise of faster and more efficient mining was too significant to ignore, and by early 2016, the first ASICs tailored for X11 began to emerge.
These machines, with their specialized architecture, could mine X11 coins at speeds unimaginable to regular GPU and CPU miners. The very thing that X11 sought to avoid – ASIC dominance – was becoming a reality.
The Impact on the Mining Community
The introduction of X11 ASICs had profound implications for the mining community. Individual miners, who once had a fighting chance with their GPUs and CPUs, found themselves outpaced and outmatched. The dream of a decentralized mining community, where everyone had an equal shot, seemed to be slipping away.
Mining pools, where multiple miners combined their computational power to mine coins, became more prevalent. While these pools offered individual miners a better chance against ASICs, they also led to further centralization, with a few large pools controlling significant portions of the network’s hashing power.
Adapting to the New Reality
While the rise of ASICs was a blow to the ideals of X11, it wasn’t the end of the road. The crypto community is nothing if not resilient. Recognizing the new reality, many miners and enthusiasts began to adapt.
Some sought to develop new algorithms and coins that could once again promise ASIC resistance, while others focused on optimizing the X11 mining process, ensuring that it remained as democratic as possible despite the ASIC dominance.
Moreover, the conversation began to shift from mere resistance to ASICs to finding ways to integrate them responsibly into the ecosystem. Ideas like making ASICs more accessible to the average miner and ensuring a more equitable distribution of mining hardware were discussed.
A Legacy of Innovation
While X11 may not have permanently staved off ASICs, its legacy is undeniable. It sparked a conversation about the values at the heart of the cryptocurrency movement and spurred further innovation in the quest for decentralization.
The story of X11 serves as a reminder that in the world of technology, change is the only constant. But with each challenge comes an opportunity for growth, adaptation, and renewed commitment to the ideals that started it all.
Cold Storage: The Ultimate Safety Vault
In the dynamic world of cryptocurrencies, where market fluctuations and technological advancements are the norms, the security of one’s assets remains a paramount concern. As we’ve journeyed through the evolution of X11 and its challenges, it’s clear that safeguarding digital assets is as crucial as ever. Enter cold storage, the digital equivalent of a high-security vault.
Understanding Cold Storage
At its core, cold storage refers to keeping a reserve of cryptocurrency offline. Unlike hot wallets, which are connected to the internet and are susceptible to hacks, cold storage solutions are completely offline, ensuring a layer of security that’s tough to breach.
There are various forms of cold storage, including:
- Hardware Wallets: Physical devices that store a user’s private keys offline. Popular examples include the Ledger Nano S and Trezor.
- Paper Wallets: A physical document containing a user’s public and private keys. It can be generated offline and then printed or written down.
- Air-gapped Computers: Computers that have never been connected to the internet, used exclusively for cryptocurrency transactions.
The Need for Cold Storage in the X11 Ecosystem
Given the ASIC dominance in the X11 mining scene, large amounts of X11 coins can accumulate in the hands of a few. This concentration makes these entities prime targets for malicious actors. Cold storage, in this context, becomes not just a luxury but a necessity.
Moreover, with the increasing value and acceptance of X11 coins like Dash, the stakes are higher than ever. Ensuring that these assets are safe from potential threats is of utmost importance.
Implementing Cold Storage: Best Practices
- Regular Backups: Whether it’s a hardware wallet or a paper wallet, regular backups ensure that even if the primary storage is lost or damaged, the assets remain safe.
- Multi-Signature Protection: This requires multiple private keys to authorize a transaction, adding an extra layer of security.
- Safe Physical Storage: If using paper wallets or hardware devices, storing them in a secure location like a safe or a safety deposit box is crucial.
- Regular Software Updates: For hardware wallets, ensuring that the software is up-to-date can protect against potential vulnerabilities.
- Avoid Public Exposure: Keeping the details of one’s cold storage solutions private minimizes potential threats.
The Future of Cold Storage and X11 Coins
As technology continues to advance, so will the methods to ensure the safety of digital assets. Biometric security, quantum-resistant algorithms, and decentralized storage solutions are just a few of the innovations on the horizon.
For X11 coins, which have already seen so much evolution and change, the journey towards optimal security is ongoing. But with the combined efforts of developers, miners, and enthusiasts, the future looks promising.
Steps to Store X11 Coins in Cold Storage
As the digital currency landscape continues to evolve, the methods and precautions for storing assets securely have become more sophisticated. For holders of X11 coins, understanding the steps to effectively use cold storage is crucial. In this section, we’ll provide a step-by-step guide to safely store X11 coins in cold storage.
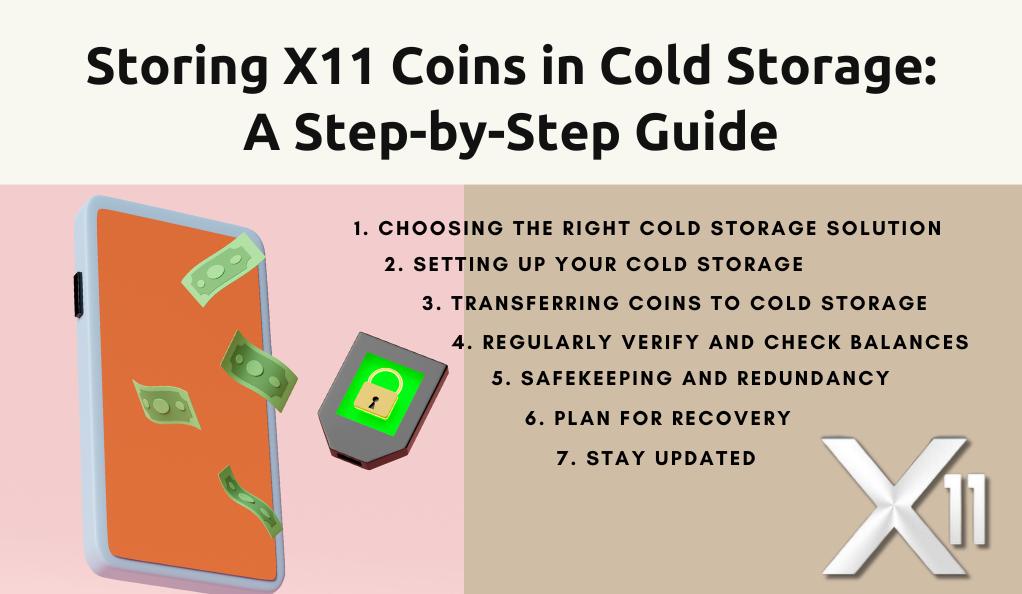
1. Choosing the Right Cold Storage Solution
Before diving into the specifics, it’s essential to select the most suitable cold storage method for your needs:
- Hardware Wallets: Ideal for those who plan to hold a significant amount of cryptocurrency and want a balance between accessibility and security.
- Paper Wallets: Best for those who intend to hold their coins for a long time without accessing them frequently. It’s the most “offline” method but requires careful handling and storage.
- Air-gapped Computers: Suitable for tech-savvy individuals who want complete control over their storage environment.
2. Setting Up Your Cold Storage
- Hardware Wallet:
- Purchase from a reputable source to avoid tampered devices.
- Initialize the wallet offline, noting down the recovery seed provided.
- Set a strong, unique pin for device access.
- Paper Wallet:
- Use a trusted online generator, ideally while offline or on a secure, malware-free computer.
- Print or write down the public and private keys. Ensure multiple copies for redundancy.
- Air-gapped Computer:
- Use a clean computer that has never been connected to the internet.
- Install a secure operating system and a wallet compatible with X11 coins.
- Generate your wallet’s public and private keys.
3. Transferring Coins to Cold Storage
- Ensure that the cold storage solution is set up correctly.
- Initiate a transfer from your online wallet or exchange to the public address of your cold storage.
- For added safety, start with a small amount to ensure the transfer process works smoothly.
4. Regularly Verify and Check Balances
- Use blockchain explorers or dedicated tools to check the balance of your cold storage without accessing the private key.
- Periodically verify the integrity of your storage solution, especially if it’s a physical medium like paper.
5. Safekeeping and Redundancy
- Store your cold storage solutions (like paper wallets) in a safe, dry place. Consider using safes or safety deposit boxes.
- Maintain multiple copies or backups in different locations to safeguard against loss or damage.
6. Plan for Recovery
- Ensure that you have a clear recovery process in case of device failure, loss, or other unforeseen events.
- Familiarize trusted family members or partners with the recovery process, especially if the holdings are substantial.
7. Stay Updated
- Technology and security landscapes change. Regularly update yourself on the best practices for cold storage and any potential threats or vulnerabilities.
Risks and Precautions
While cold storage offers a robust solution for safeguarding X11 coins and other cryptocurrencies, it’s essential to be aware of potential risks and the measures to counteract them. No system is entirely foolproof, but with the right precautions, the vulnerabilities associated with cold storage can be minimized.
| Risks | Precautions |
|---|---|
| Physical Damage or Loss | Maintain multiple backups in different locations. Consider laminating paper wallets or using waterproof/fireproof containers. |
| Human Error | Double-check all transaction details. Securely record passwords and access details separately from the primary storage. |
| Technological Obsolescence | Stay updated with technological advancements. Periodically transfer assets to newer storage solutions if needed. |
| External Threats | Maintain discretion about crypto holdings. Use safes or safety deposit boxes for added security. |
| Inheritance Challenges | Set up a digital will or provide a secure method to pass on access details to trusted individuals. |
| Software Vulnerabilities | Regularly update hardware wallet software using official updates from the manufacturer. |
| Compromised Generation Tools | Generate wallets and keys offline. If using online tools, ensure they’re reputable and operate disconnected from the internet. |
Conclusion
The intricate dance of X11 coins and the evolution of cold storage solutions encapsulate the broader narrative of the cryptocurrency world: a realm of innovation, challenges, and relentless adaptation. From the inception of the X11 algorithm as a beacon of decentralization to the ever-pressing need for robust security measures, this journey underscores the importance of vigilance and foresight in the digital age.
As we stand at the crossroads of technological advancement and financial revolution, the lessons gleaned from X11’s story serve as both a reminder and a guide. They remind us of the core values that birthed the cryptocurrency movement—decentralization, security, and inclusivity. At the same time, they guide us towards a future where these principles are not just upheld but are also enhanced through continuous innovation.
In this ever-evolving landscape, one thing remains certain: the quest for a secure, decentralized financial future is a collective endeavor. It requires the collaboration of developers, miners, enthusiasts, and visionaries. And as we move forward, armed with knowledge and driven by passion, the promise of a brighter, more secure digital tomorrow beckons.
At axerunners.com, our goal is to furnish well-rounded and trustworthy information regarding cryptocurrency, finance, trading, and stocks. Nonetheless, we avoid providing financial advice and instead encourage users to conduct their own research and meticulous verification.
Read More