The world of cryptocurrency is vast and complex, with various algorithms underpinning different digital currencies. One such algorithm that has garnered attention is the X11 algorithm. This article aims to provide a comprehensive introduction to the X11 algorithm, tracing its history, its creator, and its unique features that set it apart from other algorithms.
A Brief History and the Creator of X11
The X11 algorithm was introduced in 2014 and was designed by Evan Duffield. Evan is also the core developer behind Dash (previously known as Darkcoin), which was the first cryptocurrency to implement the X11 hashing algorithm. The name “X11” is derived from the algorithm’s unique structure, which combines 11 different cryptographic hashing functions.

The Main Purpose of X11: Prevention of ASIC Miners
ASIC (Application-Specific Integrated Circuit) miners are specialized hardware designed exclusively for cryptocurrency mining. They are incredibly efficient at mining specific algorithms, often outperforming general-purpose hardware like CPUs and GPUs. While this might sound like a boon for the mining community, ASIC miners have a downside: they can lead to the centralization of mining power, as those with the resources to invest in ASICs can dominate the mining landscape.
The X11 algorithm was introduced with a primary goal in mind: to prevent the dominance of ASIC miners and ensure a more decentralized mining ecosystem. By using 11 different hashing functions, the X11 algorithm aimed to make it challenging and resource-intensive for ASIC developers to create a specialized hardware solution for it.
Why X11 was Considered ASIC-resistant
The resistance to ASIC miners was one of the standout features of the X11 algorithm. But what made X11 ASIC-resistant?
- Multiple Hashing Functions: The X11 algorithm doesn’t rely on just one hashing function; instead, it uses 11 different functions. This multi-layered approach means that an ASIC designed to mine X11 would need to handle all these functions, making the design and manufacturing process more complex and expensive.
- Adaptive and Dynamic: The combination of multiple hashing functions means that the X11 algorithm can adapt and change based on the data it’s processing. This dynamic nature makes it harder for ASICs to gain a significant advantage over CPUs and GPUs.
- Energy Efficiency: One of the criticisms of ASIC miners is their high energy consumption. The X11 algorithm, with its multiple hashing functions, was designed to be more energy-efficient, reducing the incentive for miners to switch to energy-hungry ASICs.
Comparison of X11 with Other Algorithms
| Feature | X11 | SHA-256 (Used by Bitcoin) | Scrypt (Used by Litecoin) |
|---|---|---|---|
| Number of Hashing Functions | 11 | 1 | 1 |
| ASIC Resistance | High | Low | Medium |
| Energy Efficiency | High | Medium | Low |
| Adaptability | High | Low | Medium |
Understanding ASIC Miners and Their Impact
In the intricate world of cryptocurrency, the term “ASIC” frequently emerges, often accompanied by heated debates and discussions about its implications for the broader crypto ecosystem. To truly grasp the significance of ASIC miners, it’s essential to delve deep into what they are, the potential threats they pose, and the evolving dynamics between ASIC resistance and dominance, especially in the context of the X11 algorithm.
What are ASIC Miners?
ASIC stands for Application-Specific Integrated Circuit. In the realm of cryptocurrency, an ASIC miner refers to a specialized piece of hardware designed exclusively for mining a specific cryptocurrency algorithm. Unlike general-purpose computing devices like CPUs (Central Processing Units) and GPUs (Graphics Processing Units), which can handle a variety of tasks, ASIC miners are tailored for one specific function: mining cryptocurrency at the highest possible efficiency.
Key characteristics of ASIC miners:
- High Efficiency: ASIC miners are optimized for their specific task, allowing them to mine cryptocurrencies at a much faster rate than general-purpose hardware.
- Costly Investment: Due to their specialized nature, ASIC miners tend to be more expensive than standard computing hardware.
- Limited Flexibility: While they excel at their designated task, ASIC miners cannot be repurposed for other functions or algorithms.
The Threat of Centralization in the Crypto Mining Ecosystem
The introduction of ASIC miners into the cryptocurrency landscape brought about a paradigm shift, but not without its set of challenges:
- Economic Barrier to Entry: The high cost of ASIC miners means that only those with significant capital can afford to invest in and operate them. This economic barrier pushes out small-scale miners who rely on CPUs and GPUs, leading to a concentration of mining power among a few big players.
- Geographical Centralization: ASIC miners require a lot of energy, and their efficiency can be influenced by ambient temperature. As a result, mining operations tend to cluster in regions with cheap electricity and favorable climates, leading to geographical centralization.
- Reduced Network Security: Centralization of mining power can make the network more vulnerable. If a few entities control the majority of the mining power, they could potentially collude to attack the network or validate fraudulent transactions.
The Shift from ASIC Resistance to ASIC Dominance in X11
The X11 algorithm, initially celebrated for its ASIC-resistant properties, witnessed a transformation over time:
- The Dawn of X11: When X11 was introduced, its complex combination of 11 hashing functions made it a formidable challenge for ASIC developers. The algorithm’s design aimed to keep the mining landscape decentralized and accessible to many.
- The Emergence of X11 ASICs: Despite the algorithm’s complexity, the lucrative potential of X11 mining drove innovation. By 2016, the first ASIC miners tailored for X11 began to appear, signaling a shift in the mining landscape.
- Dominance of ASICs: As more advanced and efficient X11 ASIC miners were developed, they began to outperform CPUs and GPUs by a significant margin. This shift led to ASICs dominating the X11 mining scene, pushing out general-purpose hardware and contradicting the algorithm’s original intent.
The Composition of X11: A Deep Dive
The X11 algorithm stands out in the cryptocurrency landscape, not just for its ASIC-resistant properties, but also for its intricate composition. A unique blend of 11 individual hashing functions, X11 is more than just a complex algorithm; it’s a testament to innovative cryptographic design. Let’s delve deep into the composition of X11 and understand why it’s often hailed as one of the safest hashing algorithms.
The 11 Individual Hashing Algorithms that Make Up X11
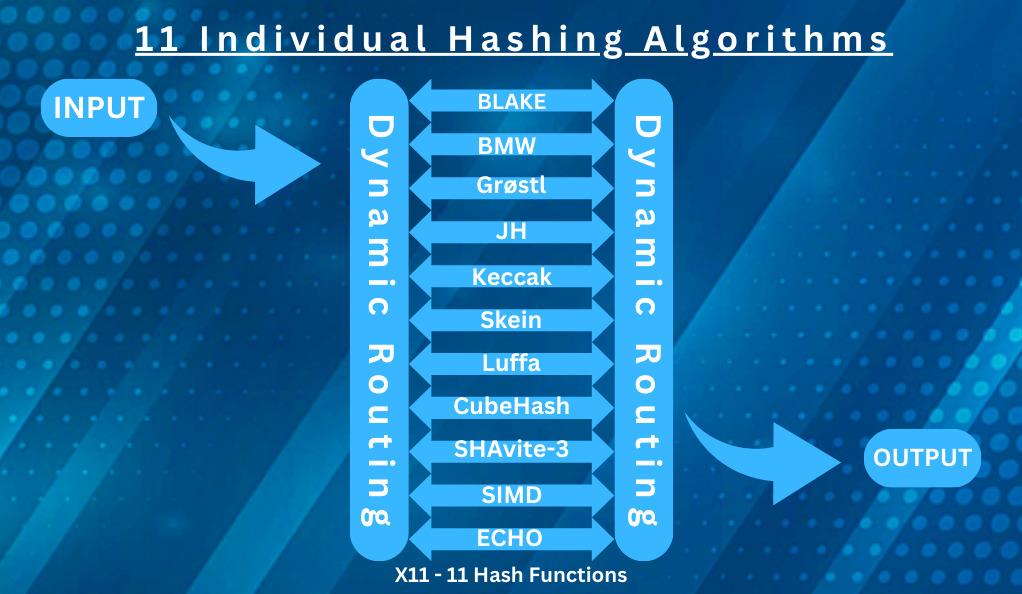
X11 doesn’t rely on a single hashing function. Instead, it combines 11 different cryptographic hashing functions in a chained manner. This means that the output of one function becomes the input for the next, creating a layered and intricate process. Here are the 11 hashing algorithms that constitute X11:
- BLAKE: Known for its high speed, BLAKE is resistant to differential cryptanalysis and offers a higher security margin.
- BLUE MIDNIGHT WISH (BMW): Efficient and fast, BMW has a complex design that contributes to the overall security of X11.
- Grøstl: Adopted by the International Organization for Standardization (ISO), Grøstl is known for its resistance to all known cryptanalytic attack vectors.
- JH: A finalist in the NIST hash function competition, JH offers both speed and security.
- Keccak: The foundation for the SHA-3 algorithm, Keccak boasts of sponge construction that provides enhanced security.
- Skein: Another finalist in the NIST competition, Skein is fast, secure, and versatile.
- Luffa: A parallelizable design, Luffa is efficient in both software and hardware implementations.
- CubeHash: A cryptographic primitive, CubeHash’s design simplicity contributes to X11’s robustness.
- SHAvite-3: With a design different from the SHA family, SHAvite-3 offers a fresh perspective and added security.
- SIMD: Stands for “Single Instruction, Multiple Data,” SIMD processes data in parallel, enhancing efficiency.
- ECHO: A NIST competition finalist, ECHO is built on a construction that combines the Merkle–Damgård structure with a unique block cipher.
Why X11 is Considered One of the Safest Hashing Algorithms
The safety of the X11 algorithm is rooted in its multifaceted design:
- Multiple Layers of Security: By chaining 11 different hashing functions, X11 ensures that even if one or a few of its functions were compromised, the entire algorithm would remain secure. An attacker would need to break all 11 functions to compromise X11, a feat that’s computationally implausible.
- Resistance to Cryptanalytic Attacks: The diverse set of hashing functions in X11, each with its own strengths and resistance to various cryptanalytic attacks, makes the algorithm incredibly resilient.
- Adaptive Complexity: The chained nature of X11 means that its complexity adapts dynamically. This adaptability makes it harder for potential attackers to predict or understand the complete hashing process.
- Energy Efficiency: While not directly a security feature, X11’s energy efficiency means that it’s more feasible for a broader range of miners to participate in the network, promoting decentralization and thereby enhancing network security.
Top X11 Coins by Market Capitalization
In the vast universe of cryptocurrencies, certain coins have distinguished themselves by adopting the X11 algorithm. Known for its unique composition of 11 hashing functions, the X11 algorithm has been the backbone for several cryptocurrencies. Let’s explore the top X11 coins by market capitalization:
1. Dash (DASH)
- Overview: Dash, originally known as Darkcoin, is the pioneer of the X11 algorithm. It’s a decentralized autonomous organization (DAO) with features like InstantSend and PrivateSend.
- Unique Features: Dash offers near-instant transactions, enhanced privacy features, and operates on a self-governing and self-funding model. It uses a combination of miners and masternodes to validate and record transactions.
2. PACcoin (PAC)
- Overview: PACcoin, or simply PAC, positions itself as the next generation digital payment network.
- Unique Features: PAC operates on a community-driven decentralized model. It focuses on low transaction fees and fast transaction times, aiming to become an efficient digital alternative to traditional currencies.
3. Polis (POLIS)
- Overview: Polis is a cryptocurrency designed for communities. It emphasizes a decentralized governance model and user-centric features.
- Unique Features: Polis operates on a masternode system, ensuring quick and secure transactions. It also has a strong focus on community involvement and decision-making.
4. MonetaryUnit (MUE)
- Overview: MonetaryUnit aims to provide a scalable and secure cryptocurrency solution that can be used for real-world applications.
- Unique Features: While it started with the X11 algorithm, MonetaryUnit has transitioned over time. It emphasizes affordability, with the vision of becoming a widely accepted means of transaction.
5. Happycoin (HPC)
- Overview: Happycoin is a digital currency designed for use in peer-to-peer transactions.
- Unique Features: Happycoin focuses on fast transaction speeds and a decentralized model. It aims to provide a user-friendly cryptocurrency experience.
6. CannabisCoin (CANN)
- Overview: As the name suggests, CannabisCoin is a peer-to-peer cryptocurrency for the cannabis community.
- Unique Features: CannabisCoin was one of the first cryptocurrencies to cater to the marijuana industry. It allows dispensaries and other businesses to transact in a more secure and decentralized manner.
7. Pura (PURA)
- Overview: Pura is an international digital currency that focuses on socially conscious value creation.
- Unique Features: Pura emphasizes autonomous funding for socially beneficial projects. It aims to create a decentralized system where communities can fund and support projects that have a positive impact.
The Decline of GPU and CPU Mining in X11
The cryptocurrency mining landscape has witnessed significant shifts since its inception. One of the most notable changes in recent years has been the decline of GPU (Graphics Processing Unit) and CPU (Central Processing Unit) mining, especially in the context of the X11 algorithm. This decline can be attributed to various factors, with the rise of X11 ASIC machines being a primary driver. Let’s delve deeper into this transition and its implications for general users.
The Rise of X11 ASIC Machines
ASIC, which stands for Application-Specific Integrated Circuit, is a type of hardware designed for a specific task. In the realm of cryptocurrency, ASIC miners are tailored to mine a particular algorithm with unparalleled efficiency. Here’s how the rise of X11 ASIC machines impacted the mining landscape:
- Superior Efficiency: X11 ASIC miners are optimized for the X11 algorithm, allowing them to mine at significantly higher speeds compared to GPUs and CPUs. This efficiency gave ASIC miners a distinct advantage, making them the preferred choice for many miners.
- Economies of Scale: As the demand for X11 ASIC miners grew, manufacturers ramped up production, leading to economies of scale. This meant that over time, ASIC miners became more affordable, further pushing GPUs and CPUs out of the market.
- Energy Consumption: Mining is an energy-intensive process. X11 ASIC miners, being optimized for the task, consume less energy per unit of work compared to GPUs and CPUs. This energy efficiency translates to lower electricity costs, making ASIC mining more profitable in the long run.
The Current State of Mining for General Users
With the dominance of X11 ASIC machines, the mining landscape for general users has transformed:
- Higher Entry Barriers: The initial investment required for ASIC mining is considerably higher than that for GPU or CPU mining. This has raised the entry barriers for newcomers, making it challenging for individual miners to start without significant capital.
- Centralization Concerns: The shift towards ASIC mining has led to concerns about centralization. Large mining farms equipped with ASIC miners have started to dominate the mining scene, leading to a concentration of mining power. This centralization goes against the decentralized ethos of cryptocurrencies.
- Reduced Profitability for General Users: For general users who still mine using GPUs or CPUs, the profitability has dwindled. Competing against the superior efficiency of ASIC miners means that these users often find their mining rewards diminishing, making it hard to cover operational costs.
- Community Initiatives: In response to the ASIC dominance, some communities have taken initiatives to keep mining accessible for general users. This includes tweaking algorithms to be more ASIC-resistant or fostering community-driven mining pools that prioritize GPU and CPU miners.
The Future of X11 Coins
Cryptocurrencies have experienced a meteoric rise in the past decade, with various algorithms and coins emerging to cater to diverse needs and niches. Among these, X11 coins have carved a unique space for themselves, thanks to their distinct algorithmic composition. As we look to the future, questions arise regarding the sustainability of X11 coins, as well as the challenges and opportunities they might encounter. Let’s explore these aspects in detail.
The Sustainability of X11 Coins in the Market
- Innovative Features: X11 coins, with Dash leading the charge, have introduced several innovative features like InstantSend, PrivateSend, and a decentralized governance system. These features, if continually updated and improved, can ensure the sustained relevance of X11 coins in the market.
- Energy Efficiency: The X11 algorithm is known for its energy efficiency compared to other algorithms like SHA-256. As global discussions around energy consumption and environmental impact intensify, X11’s energy-efficient nature could become a significant advantage.
- Diverse Cryptographic Composition: The multi-layered security provided by the 11 hashing functions makes X11 coins robust against potential vulnerabilities. This security can be a cornerstone for their long-term sustainability.
Potential Challenges
- ASIC Dominance: The rise of ASIC miners tailored for the X11 algorithm has led to concerns about centralization. If a few entities control the majority of the mining power, it could undermine the decentralized ethos of X11 coins.
- Market Volatility: Like all cryptocurrencies, X11 coins are subject to market volatility. External factors, regulatory changes, and shifts in investor sentiment can impact their market value.
- Technological Evolution: The crypto landscape is rapidly evolving. New algorithms and technologies could emerge, potentially overshadowing X11 if it doesn’t adapt and innovate.
Opportunities
- Expanding Use Cases: X11 coins can explore partnerships with businesses, online platforms, and financial institutions to increase their real-world applications and adoption.
- Community Engagement: A strong, engaged community can drive innovation, foster adoption, and act as ambassadors for X11 coins. Initiatives to involve and empower the community can be pivotal.
- Enhancing Scalability: As the user base grows, X11 coins can focus on improving transaction speeds and scalability, ensuring they remain competitive with other cryptocurrencies.
- Regulatory Collaboration: Engaging with regulators and policymakers can help shape a favorable environment for X11 coins, ensuring their growth and stability in the long run.
Conclusion
The world of cryptocurrencies is a tapestry of innovation, challenges, and constant evolution. Each coin and its underlying algorithm narrate a unique journey, reflecting the aspirations and challenges of the decentralized digital age. Among these, X11 coins stand out, not just for their intricate algorithmic design but also for the broader narrative they represent. By seamlessly integrating eleven cryptographic functions, X11 coins have demonstrated the immense potential of collaborative cryptographic principles, while also spotlighting the ongoing tug-of-war between decentralization, technological efficiency, and overarching security.
As we navigate the ever-evolving crypto landscape, the story of X11 coins offers invaluable insights. It underscores the significance of adaptability in the face of rapid technological advancements, the pivotal role of community engagement in steering the direction of a cryptocurrency, and the need for continuous innovation to stay relevant. Moreover, the journey of X11 coins serves as a reminder that in the world of digital currencies, it’s not just about creating a secure and efficient system, but also about fostering an inclusive and decentralized ecosystem that resonates with the core ethos of blockchain.
Looking ahead, while the path is riddled with uncertainties and potential disruptions, the foundational strengths, lessons learned, and the community’s resilience will undoubtedly influence the trajectory of X11 coins. Their journey, thus far and in the future, will continue to inspire and inform the broader discourse on the role and impact of cryptocurrencies in our global financial tapestry.
At axerunners.com, our goal is to furnish well-rounded and trustworthy information regarding cryptocurrency, finance, trading, and stocks. Nonetheless, we avoid providing financial advice and instead encourage users to conduct their own research and meticulous verification.
Read More